10 Tips for Choosing a Managed Service Provider (MSP)
by Patrick Hughes on October 18, 2023 at 1:00 PM
In today's fast-paced digital landscape, mastering IT management is a make-or-break deal for businesses, big and small. Wrangling your IT infrastructure can be a formidable task, draining resources and headspace.
How to Avoid Concert and Event Ticket Scams
by Nicholas Foisy on October 13, 2023 at 2:21 PM
The concert scene has been buzzing this year with top-tier performances from Springsteen, Beyoncé, Ed Sheeran, Drake, Madonna, Morgan Wallen, Metallica, and the much-talked-about Taylor Swift Eras Tour. With the constraints of the COVID-19 pandemic behind us, there's much anticipation …
The Future of Cloud Archiving: Transforming Cybersecurity & Compliance
by Alex Morgan on September 27, 2023 at 1:00 PM
Not that long ago, most records were kept in hard copy documents that were locked away in safes and filing cabinets. However, the rapid digital shift has changed the landscape significantly.
Man in the Middle (MITM) Attacks: What Are They & How to Prevent Them
by William DePalma on September 7, 2023 at 1:00 PM
In today's digital age, the confidentiality, integrity, and availability of our online communications are paramount. However, with the rise of sophisticated cyberattacks, this security is constantly under threat. One such menacing form of cyber intrusion is the man in the middle (MITM …
SOC 1 vs SOC 2 Reports - What's the Difference?
by CJ Hurd on September 1, 2023 at 3:00 PM
As the landscape of modern business shifts, one thing becomes clearer: outsourcing is not just a fleeting trend, but a strategic move adopted by companies across industries. With this increasing reliance on third-party services, there emerges an unprecedented need for more rigorous me …
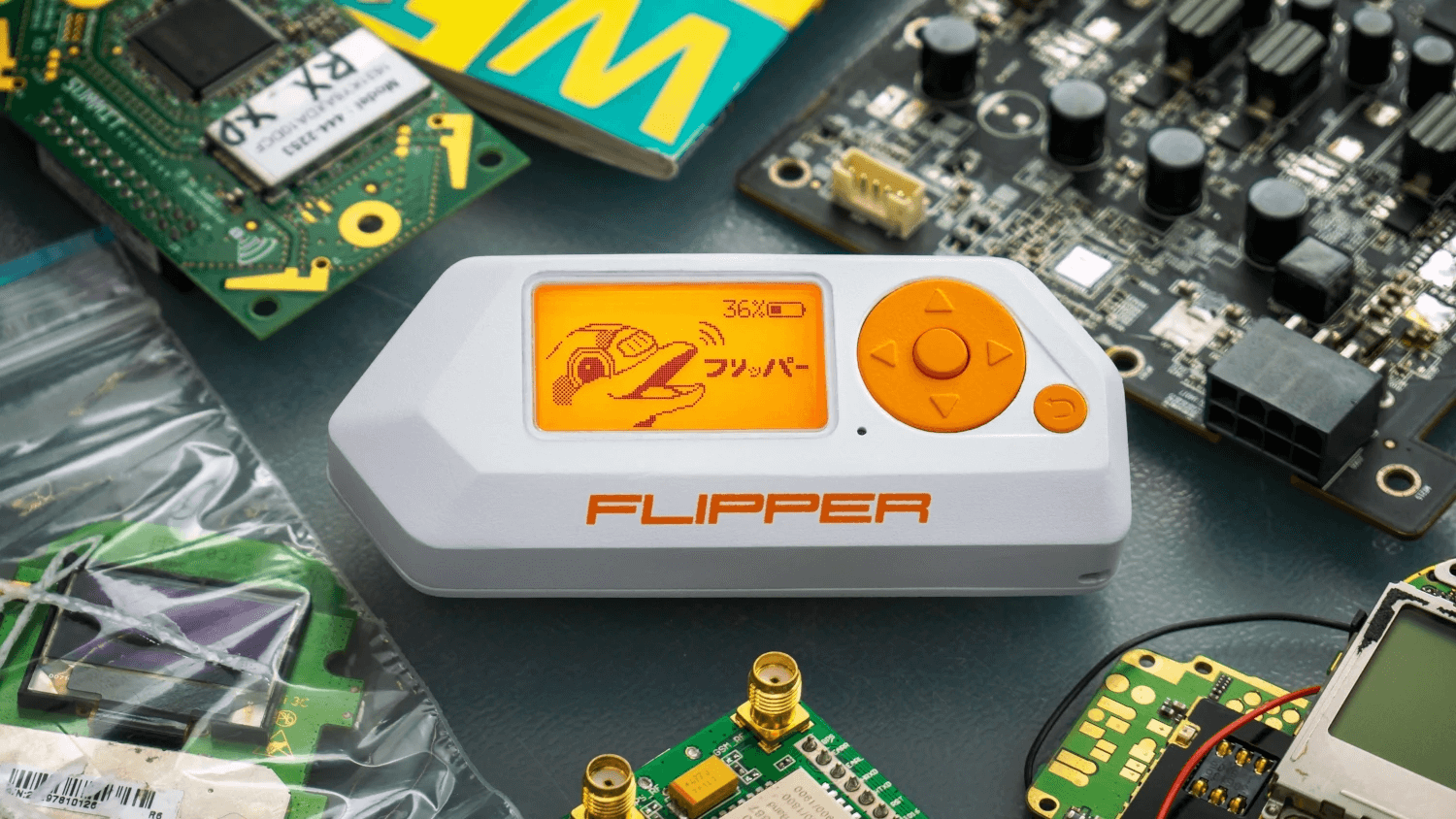
What is Flipper Zero? Portable Hacking “Multi-Tool” Explained
by Peter Fellini on August 24, 2023 at 1:00 PM
Wireless communication is integral to the modern world. Whether it is phones, Wi-Fi connectivity, or bank cards, these devices employ different types / wavelengths of wireless signals for their operations. Though infiltrating these signals traditionally demands a deep understanding of …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)