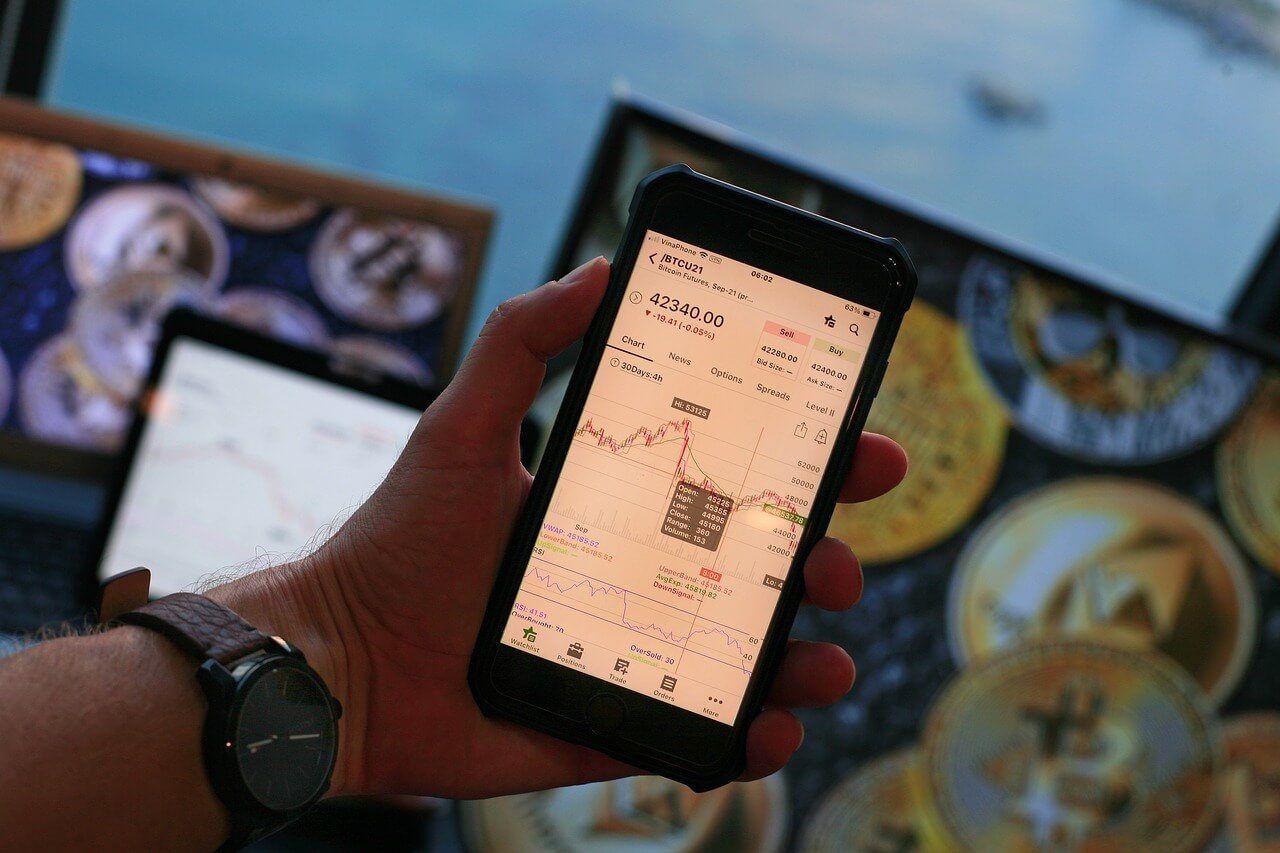
How Secure Is Your Crypto Wallet?
by Nicholas Foisy on July 7, 2023 at 12:00 PM
Over the past decade, cryptocurrency has shifted from a largely disregarded entity to a highly coveted investment class. Its appeal stems from its nature as a form of digital currency, protected by cryptography and complex computer networks, free from the influence of traditional cent …
Temu App Poses Potential Data Risk for Consumers
by Nicholas Foisy on June 30, 2023 at 11:00 AM
The modern world is governed by apps. From communication to e-commerce, every aspect of our lives seems to be tied to digital platforms that promise convenience at the touch of a button. Among these apps, a newcomer has garnered significant attention lately.
Safeguard Your Website From SEO Poisoning
by Nicholas Foisy on June 27, 2023 at 2:15 PM
In today's digital landscape, search engine optimization (SEO) plays a crucial role in enhancing a website's visibility and attracting organic traffic. However, with every advancement in technology, new risks emerge. One such risk is SEO poisoning, a deceptive technique employed by ma …
Cybersecurity Controls – Good, Cheap, Fast: Pick Two
by Mick Fitton on June 22, 2023 at 3:15 PM
Nearly twenty years ago, I was working for the public transportation department in the town where I went to school. It was there that I was introduced to the new Marketing Director, who was among the first MBAs I had met. He laid something on me that was novel to me at the time but I …
Insider Threats – Your Employee May Be Your Greatest Risk
by Jake Dwares on June 12, 2023 at 10:30 AM
In February of 2018, Ashley Liles was working as an IT Security Analyst at an Oxford based company that suffered a ransomware attack. Ashley jumped at the opportunity, not to help the company, but to enrich himself by piggybacking on the initial ransomware attack and attempting to tri …
Vishing: Over-the-Phone Scamming
by Matthew Colson on June 8, 2023 at 5:00 PM
It's always scam season, so it helps to stay vigilant all year round. Cyberattackers scarcely rest. They are constantly developing novel approaches for stealing confidential information and vast sums of money from businesses worldwide, disrupting operations and causing considerable da …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)