How Can I Hire a Virtual CISO For My Business?
by Jeffrey Torrance on February 4, 2025 at 3:15 PM
As cybersecurity threats continue to evolve, businesses—especially small and mid-sized enterprises (SMEs)—are increasingly recognizing the need for strong security leadership. However, hiring a full-time Chief Information Security Officer (CISO) may not always be feasible due to budge …
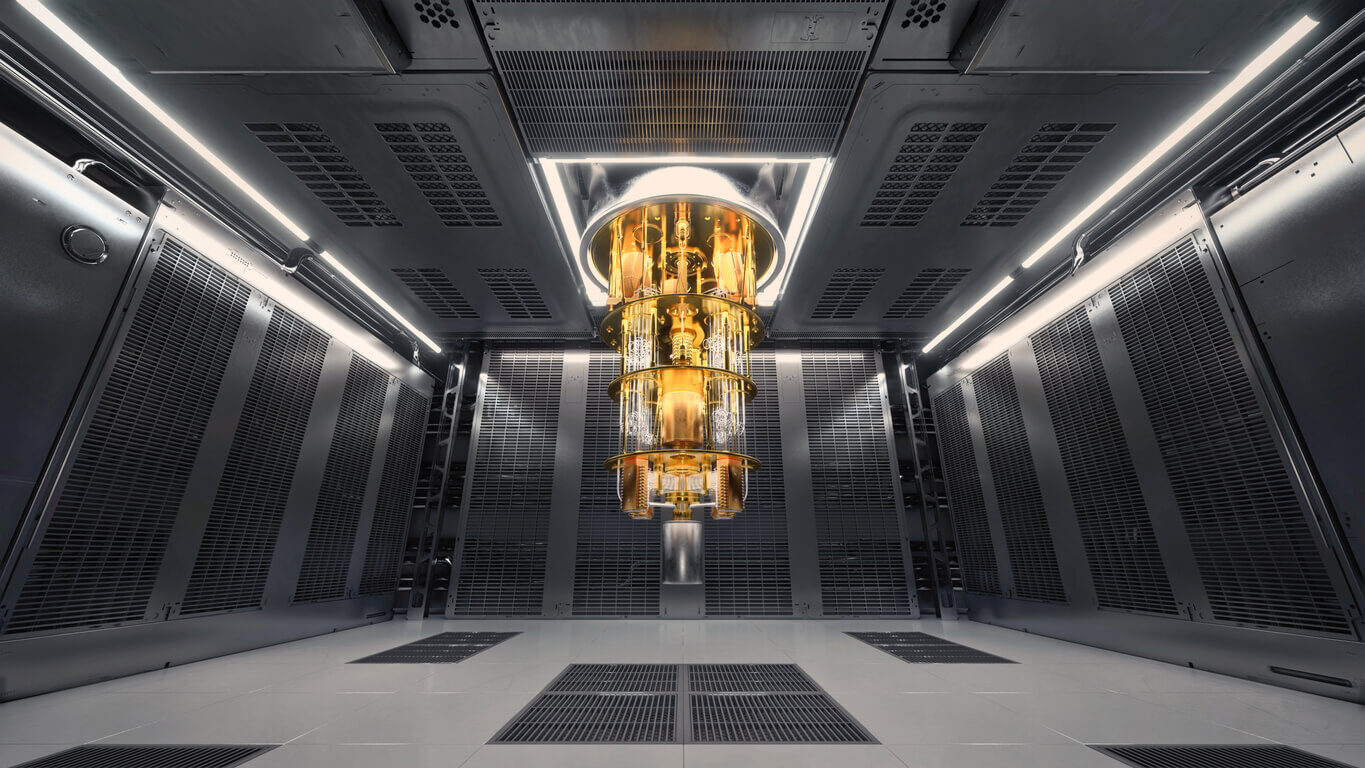
What Will Quantum Computing Mean for Passwords & Encryption?
by Nicholas Foisy on January 22, 2025 at 3:30 PM
Quantum computing is one of the most groundbreaking technological advancements of the 21st century. While its potential applications range from solving complex scientific problems to optimizing logistics, its implications for cybersecurity are profound. Specifically, the advent of qua …
Domain Name Server (DNS) Hijacking Defined
by Peter Fellini on January 6, 2025 at 11:43 AM
The Domain Name System (DNS) serves as the backbone of internet communication, translating human-readable domain names into machine-readable IP addresses. Despite its importance, DNS is often targeted by malicious actors due to vulnerabilities that can compromise its integrity. One of …
What Is the OSI Model? 7 Layers Explained
by Peter Fellini on January 3, 2025 at 11:09 AM
Networking can seem like a complex web of processes and protocols, but the OSI model simplifies this by breaking it into well-defined layers. Understanding the OSI model is essential for anyone involved in IT, as it serves as a universal framework for how data is transmitted, processe …
Here's Why Your Car Dealership Needs Cybersecurity
by Nicholas Foisy on December 9, 2024 at 2:10 PM
In previous blogs, we’ve explored TISAX and the cybersecurity challenges facing the automotive supply chain. However, there’s another critical area in the automotive sector increasingly targeted by cybercriminals: auto dealerships. As the backbone of vehicle sales and services, dealer …
Cybersecurity vs Computer Science: Which Degree to Choose?
by Nicholas Foisy on November 15, 2024 at 1:42 PM
Choosing a degree in Cybersecurity or Computer Science (CS) can be a challenging decision for many students looking to enter the tech industry. Both fields are booming, offering unique skills and career paths, but their curriculums and applications vary significantly. With the rising …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)