What Are the Best Cybersecurity Services for Protecting Sensitive Data?
by Nicholas Foisy on March 24, 2025 at 4:34 PM
Cybersecurity is no longer just a concern for large corporations and tech giants—every organization, regardless of size or industry, needs to safeguard its sensitive data. From financial records and intellectual property to customer details and employee information, the risks of a dat …
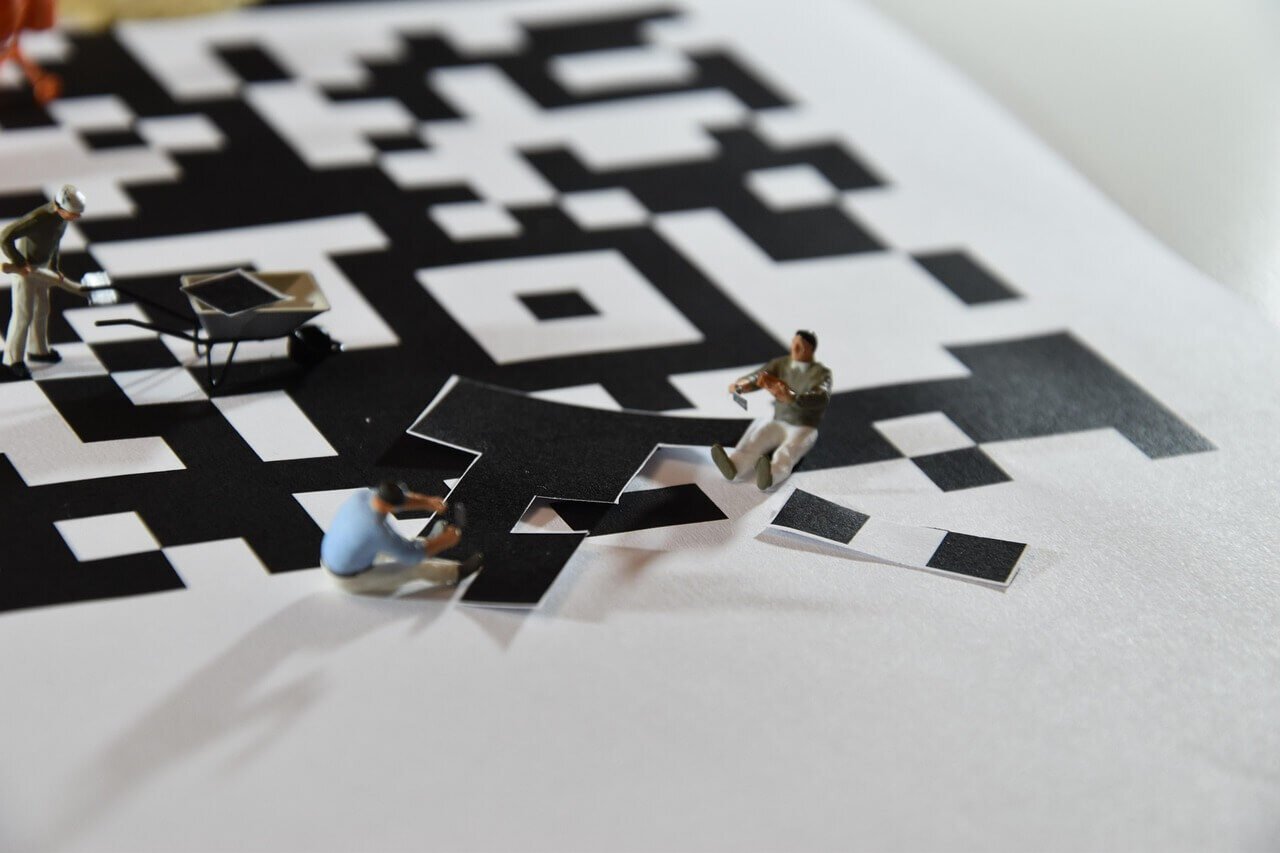
QR Code Package Scam: What You Need to Know
by Nicholas Foisy on February 14, 2025 at 1:14 PM
In recent months, reports of a new scam involving unexpected packages and QR codes have emerged, raising concerns among consumers and cybersecurity experts alike. This scam, which appears to be an evolution of the well-known "brushing" scheme, is designed to trick recipients into scan …
Cyber Insurance in 2025: Navigating Emerging Threats & Trends
by Kelly O’Brien on February 6, 2025 at 4:20 PM
As we enter 2025, the cyber insurance landscape is undergoing transformative changes driven by escalating cyber threats, shifting regulatory requirements, and evolving market conditions. Businesses must proactively stay informed on these trends to safeguard their digital assets, optim …
Physical Security Assessments: Covert Entry vs Escorted Walkthrough
by Patrick Laverty on January 31, 2025 at 1:53 PM
When businesses seek a third-party physical security assessment, they must decide on the most appropriate testing methodology to gauge their security posture. These methodologies may go by several names, but the concepts and approaches often fit into one of two categories: covert entr …
Domain Name Server (DNS) Hijacking Defined
by Peter Fellini on January 6, 2025 at 11:43 AM
The Domain Name System (DNS) serves as the backbone of internet communication, translating human-readable domain names into machine-readable IP addresses. Despite its importance, DNS is often targeted by malicious actors due to vulnerabilities that can compromise its integrity. One of …
Do SOC 2 Auditors Read and Review Code?
by Bernard Gallagher on December 26, 2024 at 1:04 PM
For organizations pursuing SOC 2 compliance, understanding the scope and focus of the audit process is crucial. A common question that arises is whether auditors review source code as part of the SOC 2 audit. Having clarity on this topic is essential, and organizations can benefit fro …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)