Understanding AI-Powered Social Engineering Attacks
by Jesse Roberts on February 13, 2024 at 4:45 PM
Social engineering manipulates people into revealing sensitive information or granting access to systems. Traditionally, it has involved phishing emails or impersonating authority figures. Today, artificial intelligence (AI) is taking social engineering to a new level. AI attackers ca …
Super Bowl Ticket Scams to Look Out For
by Nicholas Foisy on January 26, 2024 at 2:04 PM
Super Bowl ticket scams have increasingly become a prevalent issue, especially as the grandeur of the event continues to escalate each year. The allure of the NFL's biggest game attracts not only genuine fans but also opportunistic scammers looking to exploit the high demand for ticke …
How Secure Is MFA Based on SMS?
by Adam Lyford on October 27, 2023 at 1:15 PM
In an era dominated by advanced technology and an increasing number of cyber threats, ensuring the security of our personal and professional accounts has become paramount. One of the best ways to secure our accounts is through multi-factor authentication (MFA). For those who may not k …
How to Avoid Concert and Event Ticket Scams
by Nicholas Foisy on October 13, 2023 at 2:21 PM
The concert scene has been buzzing this year with top-tier performances from Springsteen, Beyoncé, Ed Sheeran, Drake, Madonna, Morgan Wallen, Metallica, and the much-talked-about Taylor Swift Eras Tour. With the constraints of the COVID-19 pandemic behind us, there's much anticipation …
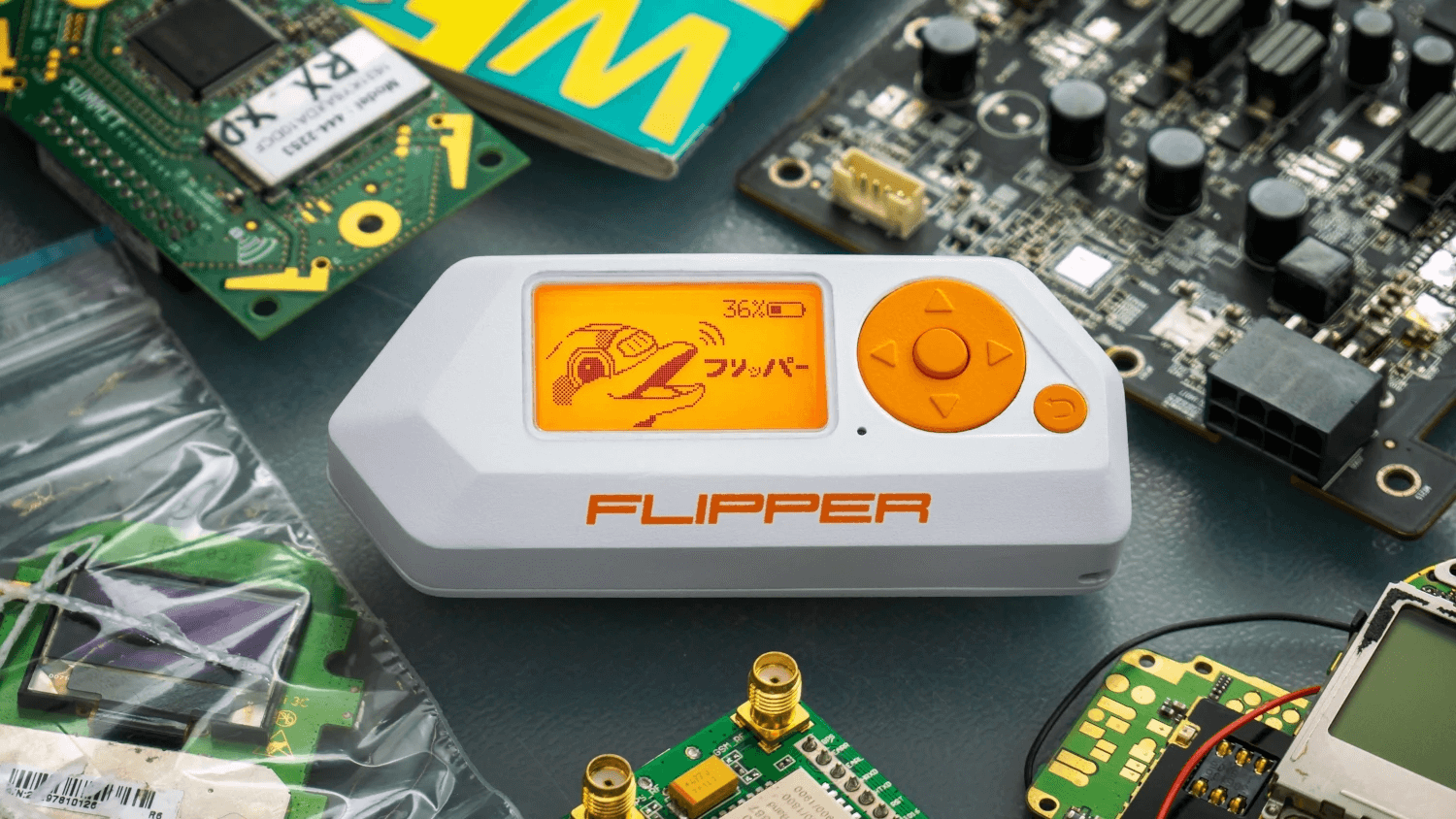
What is Flipper Zero? Portable Hacking “Multi-Tool” Explained
by Peter Fellini on August 24, 2023 at 1:00 PM
Wireless communication is integral to the modern world. Whether it is phones, Wi-Fi connectivity, or bank cards, these devices employ different types / wavelengths of wireless signals for their operations. Though infiltrating these signals traditionally demands a deep understanding of …
How Secure Is Your Crypto Wallet?
by Nicholas Foisy on July 7, 2023 at 12:00 PM
Over the past decade, cryptocurrency has shifted from a largely disregarded entity to a highly coveted investment class. Its appeal stems from its nature as a form of digital currency, protected by cryptography and complex computer networks, free from the influence of traditional cent …
.webp?width=2169&height=526&name=Compass%20regular%20transparent%20website%20(1).webp)
-1.webp?width=2169&height=620&name=Compass%20regular%20transparent%20website%20smaller%20(1)-1.webp)